Recently, a substantial leak has been brought to light, offering a rare glimpse into the ongoing hacking efforts of the Chinese government. A compilation of files and documents believed to be derived from I-Soon, a clandestine attacker affiliated with China’s government, surfaced online.
For those in the field of cybersecurity and international reconnaissance, the disclosure represents a one-of-a-kind opportunity to understand the intricate cyber operations China executes through private contractors.
An analogous incident took place in 2015, where an Italian spyware firm called Hacking Team was compromised. Much like that event, the I-Soon leakage includes internal communications and corporate data illustrating their alleged involvement in cyberattacks targeting various agencies and organizations across Asia and beyond.
The controversial documents appeared on the code repository website GitHub late last week, drawing intensive scrutiny from those monitoring Chinese cyber tactics ever since.
Jon Condra of Recorded Future, a company specializing in cybersecurity, described this as “the most significant leak associated with a business suspected of conducting cyber espionage on behalf of Chinese security services.”
John Hultquist from Mandiant, a part of the Google universe, called the leak “narrow, yet deep,” commenting on the unusual degree of transparency it provides into such secret operations.
In a detailed SentinelOne blog post, Dakota Cary remarks on this unprecedented insight into the hidden workings of a state-supported hacking vendor.
Matthieu Tartare, an analyst specializing in malware at ESET, indicated that the leakage could link some observed breaches directly to I-Soon.
Among the first to dive into the leaked content was Azaka, a Taiwanese threat intelligence researcher who shared a comprehensive analysis on X, formerly known as Twitter. This analysis reveals I-Soon’s development of intrusive tools targeting various operating systems and platforms, alongside physical hacking devices aimed at Wi-Fi networks.
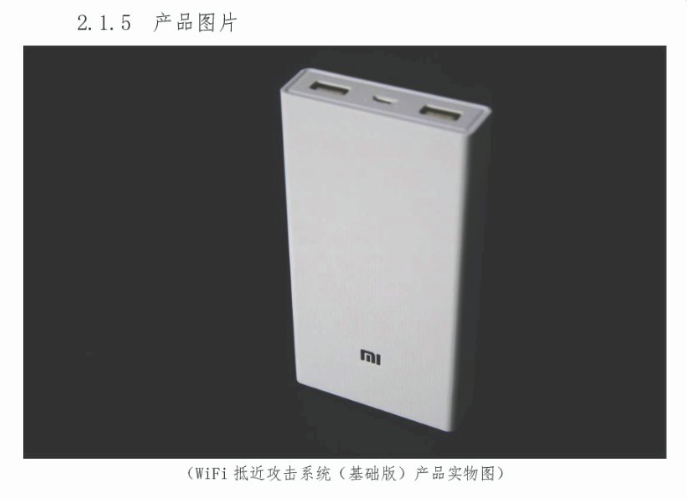
I-Soon’s “WiFi Near Field Attack System,” cunningly masked as an external battery, is used to compromise Wi-Fi networks. (Screenshot: Azaka)
Azaka’s analysis depicts how these advanced persistent threat (APT) groups operate not unlike everyday workers, though often underpaid, reflecting a reasonably extensive and profitable enterprise for breaching substantial government networks.
The leak has led researchers to connect I-Soon to Chinese state departments, including the Ministry of Public Security and the Ministry of State Security, as well as to the military. They have been noted for offering their services to target various minority groups within China.
Significantly, I-Soon is identified with APT41, a known Chinese hacking collective seen as active since 2012 and infamous for attacking sectors such as healthcare and technology on a global scale.
One revealing aspect of the leak is an IP address that previously hosted a phishing site used against Tibetans in a campaign uncovered by Citizen Lab in 2019.
Chat logs surfaced within the leak revealing the commonplace, sometimes trivial nature of the conversations between I-Soon employees, including discussions on gambling and mahjong.
Cary’s analysis points to the financial aspects revealed in the documents and chats, including the relatively low compensation of I-Soon employees.
Contact Us
Tips or further information about I-Soon or related Chinese government hacks can be shared securely with TechCrunch through various communication channels.
The leak prompts contemplation on the nature of cybersecurity economics and how emerging mercenary cyber groups could adapt and shift targets according to government commission.
While the Chinese Embassy in Washington D.C. remained unresponsive to inquiries, two anonymous I-Soon employees assured business continuity after an internal meeting on the matter.
Amidst this situation, it remains unclear who exactly posted these documents. GitHub has since removed the content from its platform, with many speculating that a disgruntled employee could be behind the exposure.
Cary stresses the leak’s intent to embarrass the company, made evident through its organizational structure, focusing on employee grievances.
FAQs about the Spyware Leak
- What is I-Soon and its connection to the Chinese government?
- I-Soon is a hacking contractor reportedly associated with the Chinese government, facilitating cyber espionage and targeted intrusions as evidenced by the leaked documents.
- What does the leaked data reveal?
- The data unveils I-Soon’s internal operations, tools for cyberattacks, targetings of certain demographics, and connections to Chinese state departments and APT41.
- How was the leak discovered?
- The leaked information was posted to GitHub and has attracted global scrutiny from cybersecurity experts.
- What is the significance of this leak?
- It brings to light the inner workings of a government-supported hacker group and allows for a better understanding of their targets, methods, and operations.
- Has there been a response from I-Soon or the Chinese government?
- No comment has been received from the Chinese government, and an email sent to I-Soon’s support has gone unanswered, although employees have been advised to continue work as usual.
Conclusion
The spillage of I-Soon’s confidential data provides an in-depth view into the hushed world of Chinese government-backed hacking activities. The detailed information serves not only as a wake-up call to potential targets but also emphasizes the complexities and risks within the cybersecurity landscape. It remains a powerful reminder of the persistent, evolving threat posed by these covert operations and the need for relentless vigilance in the defense against digital espionage.